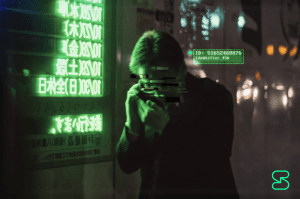
Privacy on trial: How encryption laws and backdoors threaten us all
December 04, 2020 / Alex LintonPrivate messaging, Security
“For competent authorities, access to electronic evidence is not only essential to conduct successful investigations and thereby bring criminals to justice, but also to protect victims and help ensure security.” These words — lifted from a leaked European Council memo — echo the pro-backdoor sentiments of legislatures around the world who seek to weaken encryption and endanger the privacy of their citizens to supposedly protect them from ‘criminals’.
Similar efforts can be seen worldwide, from the Five Eyes alliance bemoaning the “significant challenges to public safety” caused by end-to-end encryption, to the Brazilian “Fake News Bill” which seeks to mandate traceability in private messaging. The growing antipathy toward digital rights on display in these instances illustrates a misunderstanding of the differences between physical and digital privacy.
What's an encryption backdoor? Encryption backdoors allow someone (like a legal officer) to bypass encryption and gain access to a system — for example, to read encrypted messages.
All for one and one encryption backdoor for all
Regardless of whether you agree with law enforcement having the ability to gain access to people’s private data, the pertinent issue with all of these endeavours is the impossibility of keeping these powers only in the hands of ‘competent authorities’. To create the possibility of a third party viewing end-to-end encrypted messages defeats the entire point of encryption. If a backdoor is created for law enforcement to view private messages, there is nothing to ensure only law enforcement can use it. Anyone with either know-how or luck could discover these backdoors — and considering how lucrative such a process can be, there will always be malicious parties looking for them.
Why shouldn't we have encryption backdoors? Backdoors are actually just systemic weaknesses in the system — so anyone can exploit the weakness to bypass encryption and gain unauthorised access. This creates a huge security and privacy problem!
Too often, authorities justify compromising the privacy of their citizens with the promise of using their newfound power to catch dangerous criminals, but not only is there very little evidence that this is the case, there is a multitude of evidence that authorities will use any powers afforded to them outside the intended scope. The idea of a police officer scanning your personal messages because you got a speeding ticket would be right at home in a pulpy dystopian cyberpunk novel — it’s not something that should ever approach reality.
So, considering the glaring problems with these intrusive measures and the fervour with which they are being pushed by legislatures and regulators all over the world, what can we do about it?
The future is open-source (and decentralised)
There are two crucial features that a private messenger must have to protect users against overzealous governments.
The first: be open-source. The best protection against the creation of a backdoor is for the source code of the application to be publicly available. If it’s possible for every user to scrutinise the make-up of the app and compile it themselves, it becomes almost impossible to hide a malicious piece of code. Of course, it can still be done, which is why it’s still best practice to have a security audit — so any problems missed by the community will be found and rectified. When it comes to privacy, trust is a dirty word. An application having closed-source code means the developers are asking you to trust that there is nothing malicious going on. Open-source lets you see for yourself.
The second may be less obvious, but it is no less vital: decentralisation. The age-old problem with centralised services is that when the government decides they want a backdoor into a private messenger, they don’t ask nicely — they demand. A centralised service would then most likely have two options: comply or be shut down. Here comes that trust word again. A decentralised service has an advantage in this scenario, because there is no operating company to tap on the shoulder and shut down the service. You don’t have to trust a provider to keep their services available to you — even in the face of litigation or intimidation. Instead of one central server or server cluster for message routing, there are hundreds or thousands all around the world, outside the jurisdiction of any single governing body. And even shutting down the developers won’t stop a service that is both decentralised and open-source, as the code will still be available for anyone to compile themselves.
Privacy is not negotiable. There is no such thing as a backdoor that only law enforcement can access — if it exists at all, it exists for everyone. When seeking measures to curb criminal activity, it should be imperative that the rights of every citizen aren’t infringed — it simply isn’t worth it.
A Personal Appeal From Cofounder of Session - Chris McCabe
March 18, 2026 / Chris McCabe
Rotating keys for Session repos
January 22, 2026 / Session
Session Pro Beta update: December 2025
December 07, 2025 / Session
Session Protocol V2: PFS, Post-Quantum and the Future of Private Messaging
December 01, 2025 / Session
Removing screenshot alerts from Session
November 09, 2025 / Session
Session Pro Beta Development Update: Progress and Community Insights
October 30, 2025 / Session