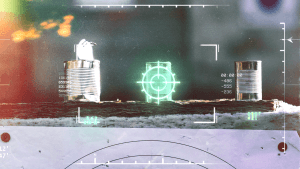
Target acquired: The increasing threat of targeted cyber-attacks
September 12, 2022 / Alex LintonPrivacy, Security
These days it feels like there are major hacks going down all the time. Data gets leaked, stolen, or just sold to the highest bidder. While these kinds of attacks affect a lot of people, they also give malicious attackers a window to perform highly sophisticated, targeted attacks. Cybercrimes have gone up 300% in the last few years alone — so how do you protect yourself?
Let's talk about the humble phone number. It's no secret that I hate the state of phone numbers in the modern world. They are a weak point in most people's personal security — a giant neon sign that gives attackers the perfect data point to target. We use phone numbers for authentication, communication, and verification, but they really haven't got the chops to be such a vital part of our security model — and it's becoming impossible to sign up for new services without a phone number.
And what does that mean for us? It means our phone numbers are being leaked all over the place, leaving people wide open for attack.
Pegasus: The spyware kind, not the flying horse kind
Last year a group of journalists working alongside the Organized Crime and Corruption Reporting Project (OCCRP) gained access to a list of 50,000 phone numbers that had been targeted by Pegasus spyware. Fifty. Thousand.
Note: Pegasus is a piece of spyware developed by the NSO Group which can be used to covertly infect and surveil mobile devices. It uses a zero-click exploit, making it extremely dangerous.
Here's the thing, this wasn't a randomly chosen group of 50,000 phone numbers. The targets were very specific — the French President, the King of Morocco, the creator of Telegram. Their phone numbers were sourced in multiple ways, often by targeting other people in their lives who probably take less stringent security measures. Sure, maybe Emmanuel Macron has high-level security training and resources. But what about a random government official at a summit? Or just, a friend? A sibling? They can be exploited instead, opening the door to the true target.
Thankfully most of the people reading this article won't be targeted by an attacker as sophisticated as the NSO, but that doesn't mean you can't be targeted.
The SIM swap
The prevalence of SIM swapping attacks has been trending upwards as we rely more and more on our phone numbers for things like 2FA. Although it targets the same point of weakness as Pegasus (the damned phone number), it works differently.
We've already covered SIM swapping attacks before, but SIM swapping has been used to target people for their fame or audience, like Twitter founder Jack Dorsey, to try and steal social media handles, or to target people who hold large amounts of cryptocurrency.
A SIM swapping group that was busted by the US Department of Justice in November 2021 was responsible for stealing tens of millions of dollars worth of crypto using SIM swapping attacks. Some of the victims were your standard mom-and-pop investors, who may have only lost a few thousand dollars — but in some cases that amounted to losing their entire retirement savings. One victim was scammed out of over 5 million dollars. Oof.
It's a super shady attack, and the only good way to protect against it is to just...not use your phone number for security purposes to begin with. Unfortunately some platforms haven't gotten the memo just yet and continue to force users into authenticating or verifying using a phone number.
Luckily apps like Session are give people the ability to ditch their phone numbers for something more secure and private. The more people do this — the better off we'll all be.
Cyber attacks overall are on the rise
With every year that goes by we rely more and more on the digital world — making it more and more lucrative for malicious attackers to try and pull off hacks. Combine that with the ever-increasing amount of personal data floating around in 'the cloud', shared on social media, or exposed through other means — and the result is an increase in the amount of successful, targeted attacks. The FBI says there has been a 300% increase in reported cybercrimes since the beginning pandemic which has resulted in trillions of dollars in damages.
For every hack that affects a million people, there are going to be a bunch of vulnerable people (that someone may want to target) who are now exposed.
The recent Twilio hack which impacted 1,900 Signal users is the perfect example of this. There were 1,900 accounts that could've been targeted by the attackers — but they were only looking for three of them.
Hackers are no doubt getting better at using the troves of data that get exposed in leaks to then weaponise against specific individuals — and this could create a very dangerous future for people like journalists, activists, and other human rights defenders.
A Personal Appeal From Cofounder of Session - Chris McCabe
March 18, 2026 / Chris McCabe
Rotating keys for Session repos
January 22, 2026 / Session
Session Pro Beta update: December 2025
December 07, 2025 / Session
Session Protocol V2: PFS, Post-Quantum and the Future of Private Messaging
December 01, 2025 / Session
Removing screenshot alerts from Session
November 09, 2025 / Session
Session Pro Beta Development Update: Progress and Community Insights
October 30, 2025 / Session